SOFTWARE APPS AND LIBRARIES
Commercial National Security Algorithm Suite 2.0 (CNSA 2.0)
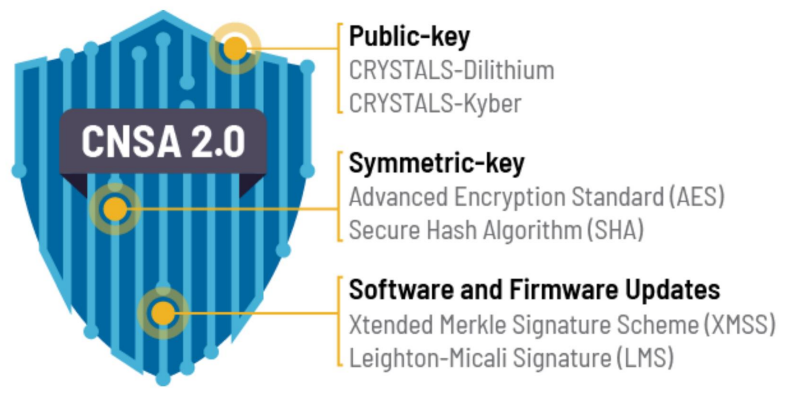
NSA recommends adopting the CNSA 2.0 software & firmware signing algorithms immediately.
Arkham Technology IP are developed under NSA requirements; they are evaluated and used in NSA certified high-assurance solutions:
ML-DSA (CRYSTALS – Dilithium) - Level 2, 3, 5 SW
ML-KEM (CRYSTALS – Kyber) - Level 1, 3, 5 SW
SHA-3 (Keccak) SW
SHA-256, 384, 512 FW
AES-256 FW
Contact Us for:
Xtended Merkle Signature Scheme (XMSS)
Leighton-Mical Signature (LMS)
High-Assurance Randomizer, classified & unclassified “Suite-A” algorithms
SOFTWARE BENEFITS
Cutting-Edge Software Solutions for Advanced Cyber Defense Security
Technology
Unique licensable Intellectual Property (IP) for high-assurance cryptographic modernization and KMI Integration.
Security
Cleared staff and secure development infrastructure certified and accredited by the U.S. Government for trusted microelectronics design.
Quality
Mature engineering and development processes compliant with U.S. and international standards to ensure quality.
Expertise
Successful design, certification, and integration support of over 25 different
high-assurance COMSEC and KMI systems.
HOW IT WORKS
How Our Software Enhance Cyber Defense Security
Assessment and Analysis
Our system conducts a thorough assessment of your network infrastructure to identify vulnerabilities and potential threats. Using advanced algorithms, we analyze data to understand your specific security needs.
Customized Solution Deployment
Based on the assessment, we deploy tailored software apps and libraries that fit your unique security requirements. This ensures optimal protection and integration with your existing systems.
Real-Time Monitoring
Our tools continuously monitor your network in real-time, detecting suspicious activities and anomalies. This proactive approach helps in identifying threats before they can cause harm.
Threat Detection and Response
When a threat is detected, our software immediately triggers an alert and initiates automated response protocols. This includes isolating affected areas and mitigating risks to prevent data breaches.
Continuous Updates and Improvements
We regularly update our software apps and libraries to stay ahead of emerging cyber threats. Our dedicated team works around the clock to enhance security features and implement the latest defense technologies.
Comprehensive Reporting and Analytics
Gain insights into your security posture with detailed reports and analytics. Our tools provide comprehensive data on threat patterns, system performance, and the effectiveness of implemented security measures.

